cyber security aCTION PLAN
Understand your cyber risk. Know exactly what to do next.
Create your board-ready cyber risk roadmap in 3 weeks.
What you get
A fixed scope, fixed price engagement that delivers leadership-level clarity on cyber risk, priorities, and next actions. We call this your Cyber Risk Compass.
Business impact analysis
Understand what would cause real operational, financial, or reputational damage if it went wrong.
Ranked cyber risk register
Your key cyber risks clearly identified and prioritised so you know what matters most.
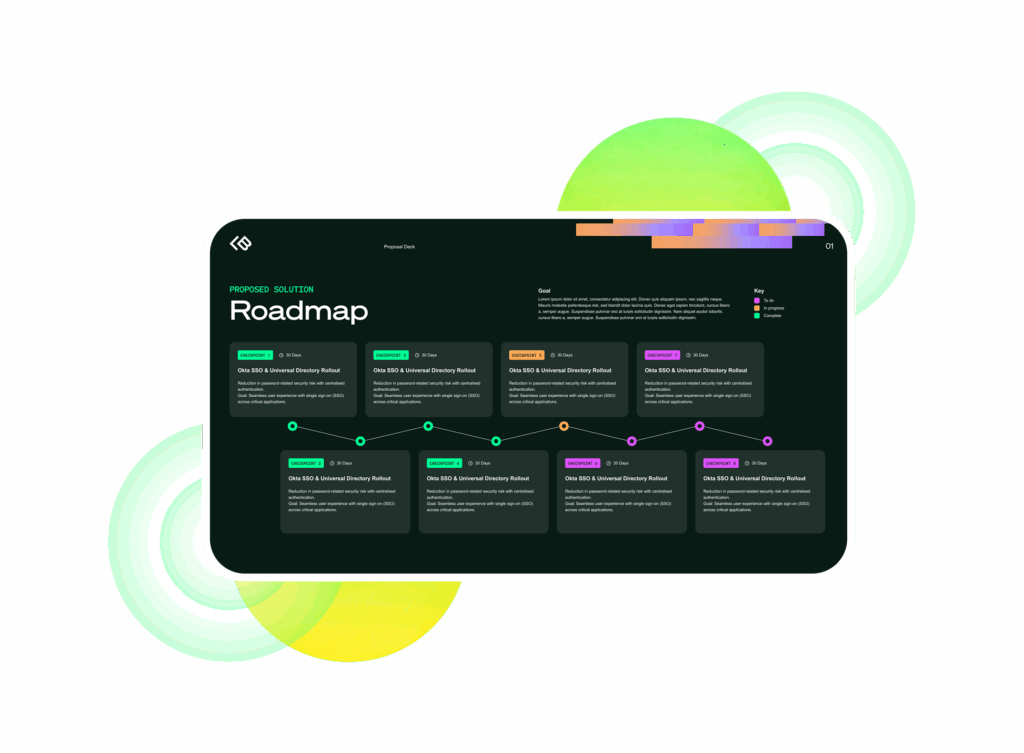
Prioritised action roadmap
A practical plan showing what to fix first, what can wait, and how to reduce risk quickly.
Investment clarity
Create clear links between security spend to real risk reduction, so you can invest with confidence.
Governance that lasts
Define ownership, reporting, and cadence to keep cyber risk under control long after the cyber compass project ends.
Board-ready insight
A concise, decision-ready summary of risks, priorities, costs, and next steps.

What makes it different?
This is a clear actionable plan, not just another technical report. Gain a clear, business-led view of your cyber risk and the decisions needed to reduce it. Built for leadership, the outcome is clarity for the board, direction for your teams, and governance that lasts beyond the project.
Board-led not tool-led
We start with business impact and risk appetite — not technology shopping lists.
Designed for decision-making
Outputs are structured so leadership can approve priorities and investment with confidence.
Independent oversight
We validate reality, reduce blind spots, and ensure delivery stays accountable.
Focus effort where it matters most
We identify the handful of actions that remove the most risk first.
Build towards recognised standards
Establish the foundation for ISO 27001, investor due diligence, and security maturity.
Fixed scope, fixed price
Clear outcome. Clear timeline. No open-ended consulting.

How we work
We work collaboratively with leadership and IT to quickly understand your business, assess cyber risk in practical terms, and deliver a clear, prioritised plan for reducing it.
Discover & understand
We host short, focused workshops with leadership and IT to understand your business operations, critical systems, and what disruption would actually mean in financial and operational terms.
Assess risk & identify priorities
We analyse your current security posture, identify key risks, and build a prioritised risk register. We focus on the small number of actions that reduce the most risk first.
Deliver a board-ready roadmap
We translate the findings into a clear cyber risk plan with prioritised actions, governance guidance, and an executive readout so leadership can confidently decide what to do next with the option for us to support with implementation or for your team to take forward.
“It’s a tremendous thing not to worry. When I hand a project over to LeftBrain, I know it will just get done. There is so much value in that level of trust.”

FAQs
You’ll receive a board-ready cyber risk plan with a prioritised list of actions and requirements, clearly outlining the decisions needed. The goal is simple: clarity on where you stand and what to do next.
You leave with a clear, prioritised roadmap your team can execute. If you want support, we can help with implementation oversight or ongoing vCISO guidance, but there’s no obligation and you can use this plan with your existing service provide if you wish to.
The engagement is fixed-scope and fixed-price, so there are no surprises. Pricing depends on the size and complexity of your organisation, but it’s designed to be a small investment compared to the cost of implementing the wrong security priorities.
Very little. Most of the work happens through a small number of structured workshops and information reviews. Typically, we need a few hours from leadership and your IT provider to understand the business, current environment, and priorities.
No (not unless you want it to!). Our role is to provide independent oversight and strategic direction, ensuring security priorities are clear and that implementation is aligned with real risk.
The Cyber Risk Compass is designed to be fast and focused. Most engagements are completed in around three weeks, giving leadership a clear picture of risk and a prioritised plan without long consulting projects.
Take cyber risk from fear to clear with a plan that works.
Whether you’re scaling fast, aiming for certification, or navigating complex risks, we’ll work with you to build a security strategy that fits how your team works and supports the future you’re building.




