It’s 2009. Picture it. A cluttered office, PC towers propping up the desks. A worker reaches over a stuffed in-tray and dials down the radio; the latest Beyonce hit “Ohh, you gotta put a ring on it…” fades to below the sound of the server fans.
“I… Err. Clicked on this link,” he says, slumping back into his chair. “I thought it was. Odd. There were typos; I thought, Microsoft don’t make typos… do they?”
He winds the cord around his finger.
“Yes,” he says. “‘I. I entered my email. My password. Uh-huh. Yeah, nothing happened. Just. Just a blank page.”
This conversation is familiar. What happens next is a frantic scramble to implement the golden unicorn of online account security – Multi Factor Authentication (MFA). Text messages and time based codes pursue, then everything is safe again. But it’s not 2009 anymore, it’s 2024. More accurately, it’s post EvilGinx3. So, what has changed?
The hackers have had many years to think of creative ways to get around MFA. There’s been some secret hacker meeting and the board have settled on one great solution – instead of capturing credentials, which aren’t enough when MFA is enabled, they decide to focus on capturing the session token (the cookie that your browser receives after you’ve authenticated). That way you don’t need to try to login, you can just pop this token in your own browser, refresh the page and be logged in as the victim. Easy. What’s more the hacker consortium tech department has stumbled upon a very useful tool to aid with this. It’s called EvilGinx, a ‘reverse-proxy phishing toolkit’ that captures these tokens. Great! Also, it’s on GitHub, free to download and use. Someone with very little technical knowledge can have a working phishing site, capable of bypassing MFA, in a matter of hours. Mic drop. Meeting adjourned.
Quick aside:
How does reverse-proxy work? This is supposed to be an article for non-technical folk.
Well, let me try and explain it simply:
Instead of a hasty, grammatically terrible fake site, a reverse-proxy phishing site is sort of like a pane of glass. You hit it and there behind it is the real login window, but you can’t see the glass, it’s so clean. You enter your credentials, you respond to your MFA prompts, and behind the glass you get logged in and you browse away without ever noticing there’s something in the way. Except the glass has some clever secret agent stuff; it makes a copy of your session token as it passes through it. The hacker then takes it and has full access to your account.
This tool isn’t new. It’s actually been around since 2017, but it’s now (perhaps since the v3 release) become mainstream. There are several popular ways this is being used that are alarming:
- The compromised account is used to spread it further. The attacker sends another phishing email to everyone in the contacts, spraying it far and wide. This is noisy and is spotted easily. The goal here is to harvest as many stolen sessions as possible. It’s sort of like the old Stuxnet Virus. Spread it far and wide and you might capture someone really interesting.
- Targeted financial fraud: once in the account of an important person, the attacker targets the accounts team and the CFO with bogus invoices.
- Full on havoc: the attacker steals data, extorts its victim, sells its secrets and seeks to destroy the reputation of the business (unless they cough up).
- Spying on important people: Check out this advisory from the NCSC that mentions EvilGinx by name.
So, stopping it…
The concept is actually pretty simple: introduce an out of bounds authentication event.
Let me explain: that glass you’re looking at, what if the website on the other side said, “Hey, don’t look at me to authenticate, turn around and look at another site. And if that other site is happy, it’ll send you back here. TTFN.” So the user turns around, a full 180, does the authentication, then that ‘friendly’ site returns them to the real site. The piece of glass is left hanging, “Uhh, where did everyone go?”
Now, the nitty gritty: what is an out of bounds event?
- Federated identity. If you use a service like Okta, OneLogin, Jumpcloud (note, these can also be phished but it’s much more complex, and when combined with 2 or 3 that risk can be mitigated).
- Things that use the WebAuthn protocol: Things like TouchID, Windows Hello, Yubikey, Passkeys.
- Third Party MFA. Services like Duo that redirect your MFA request in a manner similar to federated identity.
Which is best? Number 2 is great, but it’s longer / harder to implement. Number 3 is quick, easy and low cost. Number 1 with 2 or 3 is ideal. Do whatever works best for your business, just don’t leave your authentication all in one place.
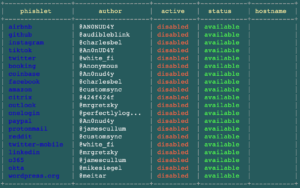
So that’s it. I’ll leave you with a screenshot of EvilGinx so you can see what things are exceptionally vulnerable to this (note: these are the standard ‘phishlets’ and the services most at risk, but there are others).
Here you go…
Disclaimer: The mitigations mentioned here worked when we tested them. Things change and attackers evolve, do your own testing. Some mitigations (2 and 3) prevent session token capture, but your password is still captured.
Let’s get started
We work with fast-moving innovative teams who expect clarity, pace and iteration. If you’re scaling fast and want delivery partners who truly work like you do, we’d love to help.